
Ukrainian hackers hacked into Russian military accounts and gained access to the monitoring systems used by drone operators. This allowed them to determine how Russians are using Belarusian infrastructure to attack Ukraine.
The cyber operation was carried out by hackers from the Fenix cyber analytics center in cooperation with the international intelligence community InformNapalm.
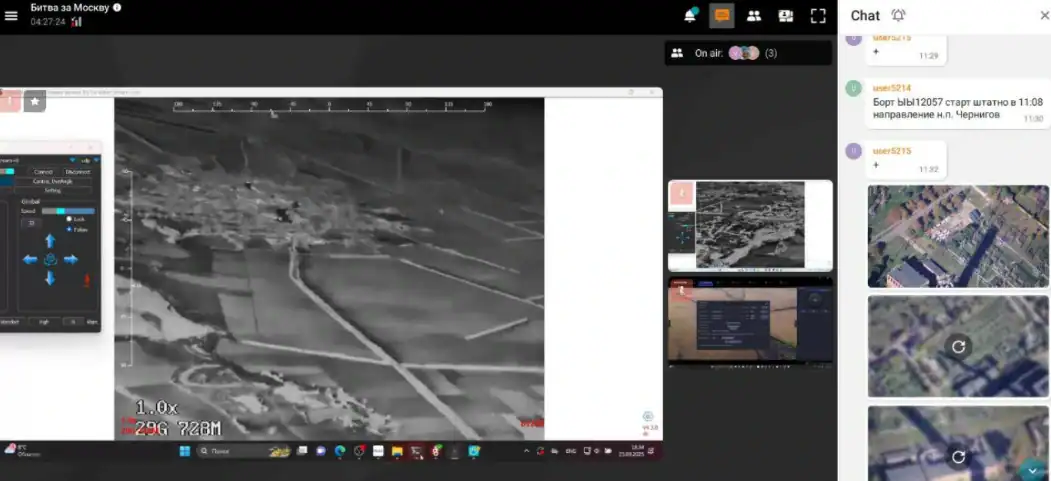
During the operation, cyber experts hacked into the accounts of dozens of Russian military personnel and gained access to the monitoring systems used by drone operators.
Ukrainian hackers did not control the drones, but they were able to see the enemy’s actions and contribute to the effectiveness of the Ukrainian side’s countermeasures.
Intelligence officers organized round-the-clock covert surveillance of the accounts, during which data was promptly transmitted to the Ukrainian Defense Forces. This significantly improved the situational awareness of Ukrainian defenders and enabled them to effectively shoot down and suppress Russian drones.
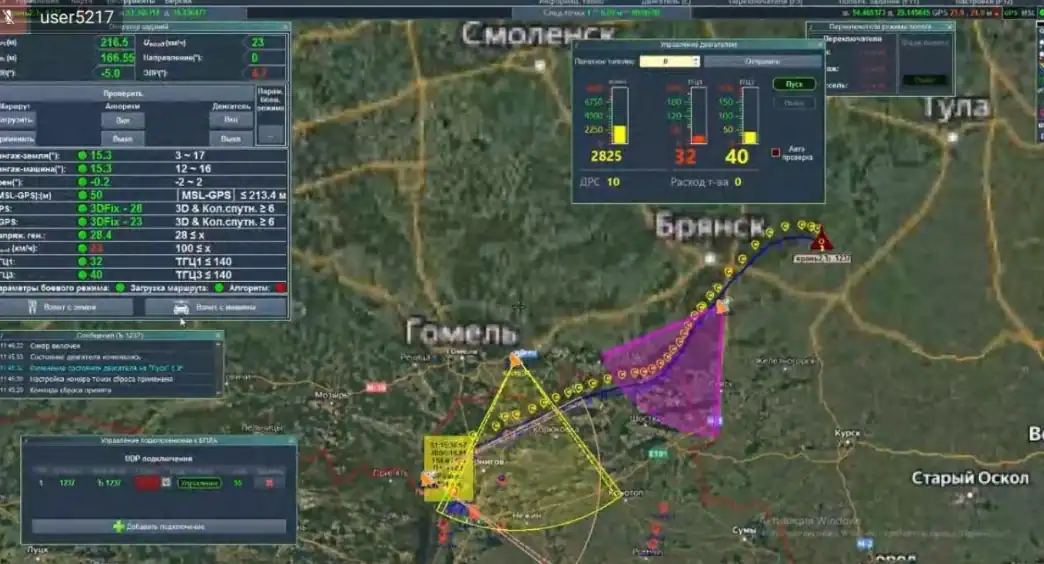
As of September 2025, while analyzing data intercepted in Russian operators’ chat rooms, analysts found that Russia actively uses civilian infrastructure, in particular cell towers on the territory of Belarus, to lay routes for its drones.
In this way, the Russians ensured a stable signal for striking targets located on the northern and western borders of Ukraine, and even flew into the territory of NATO countries.
At the same time, in September 2025, analysts provided operational information to NATO partners that the flight of dozens of Russian drones in Poland on the night of September 9-10, 2025, was part of testing new tactics and capabilities of Belarusian civilian cellular infrastructure.
The Russians then planned to strike logistics routes in both Ukraine and Poland to cut Ukraine off from Western weapons and equipment supplies.
In total, the cyber operation lasted more than six months and, as of February 2026, had exhausted its operational reconnaissance capabilities, in particular as a result of the successful implementation of a series of operations by the Ukrainian Defense Forces.
In particular, the Defense Forces carried out effective strikes on command posts and drone launch sites in Russia and the temporarily occupied territories of Ukraine, as well as on locations of the elite Russian Rubicon unit.
The culmination of the long-term cyber operation was the sanctions announced on February 18, 2026, by Ukrainian President Volodymyr Zelensky against Belarusian dictator Alexander Lukashenko for his involvement in escalating and prolonging the war of the aggressor country, Russia.
As emphasized by the InformNapalm intelligence community, the experience of this and many other successful cyber operations has proven that deep penetration into the enemy’s communications, planning, and coordination systems has a significant impact on the course of hostilities.
Підтримати нас можна через:
Приват: 5169 3351 0164 7408 PayPal - [email protected] Стати нашим патроном за лінком ⬇
Subscribe to our newsletter
or on ours Telegram
Thank you!!
You are subscribed to our newsletter